Title
Topic
-
Hajjar receives leadership award for contributions to civil engineering education
“The American Society of Civil Engineers (ASCE) has awarded … Jerome F. Hajjar, CDM Smith Professor and chair of the department of civil and environmental engineering at Northeastern University, the 2023 Thomas A. Lenox Excellence in Civil Engineering Education (ExCEEd) Leadership Award for extraordinary leadership in civil engineering education. The award was presented at the Civil Engineering Division Banquet at the 2023 Annual Conference of the American Society for Engineering Education in Baltimore, Maryland.”
-
Developing new generation of intelligent tutoring systems for advanced manufacturing
“Mechanical and industrial engineering assistant professor Mohsen Moghaddam is leading a $850K NSF grant for ‘Accelerating Skill Acquisition in Complex Psychomotor Tasks via an Intelligent Extended Reality Tutoring System.’ Project collaborators include Northeastern University co-principal investigators Kemi Jona, assistant vice chancellor for digital innovation and enterprise learning, Casper Harteveld, associate professor of game design and associate dean of the College of Arts, Media and Design and Mehmet Kosa, postdoctoral research associate working with Casper. This project builds upon the ongoing research of the PI at the intersection of AI and augmented, virtual, and mixed reality, sponsored by NSF, DARPA, and…
-
Air Force Office of Scientific Research provides $540K grant for video anomaly detection
“Electrical and computer engineering and Khoury College of Computer Science professor Yun Raymond Fu received a $540,000 Air Force Office of Scientific Research grant to address video anomaly detection through deep learning and perturbation techniques.”
-
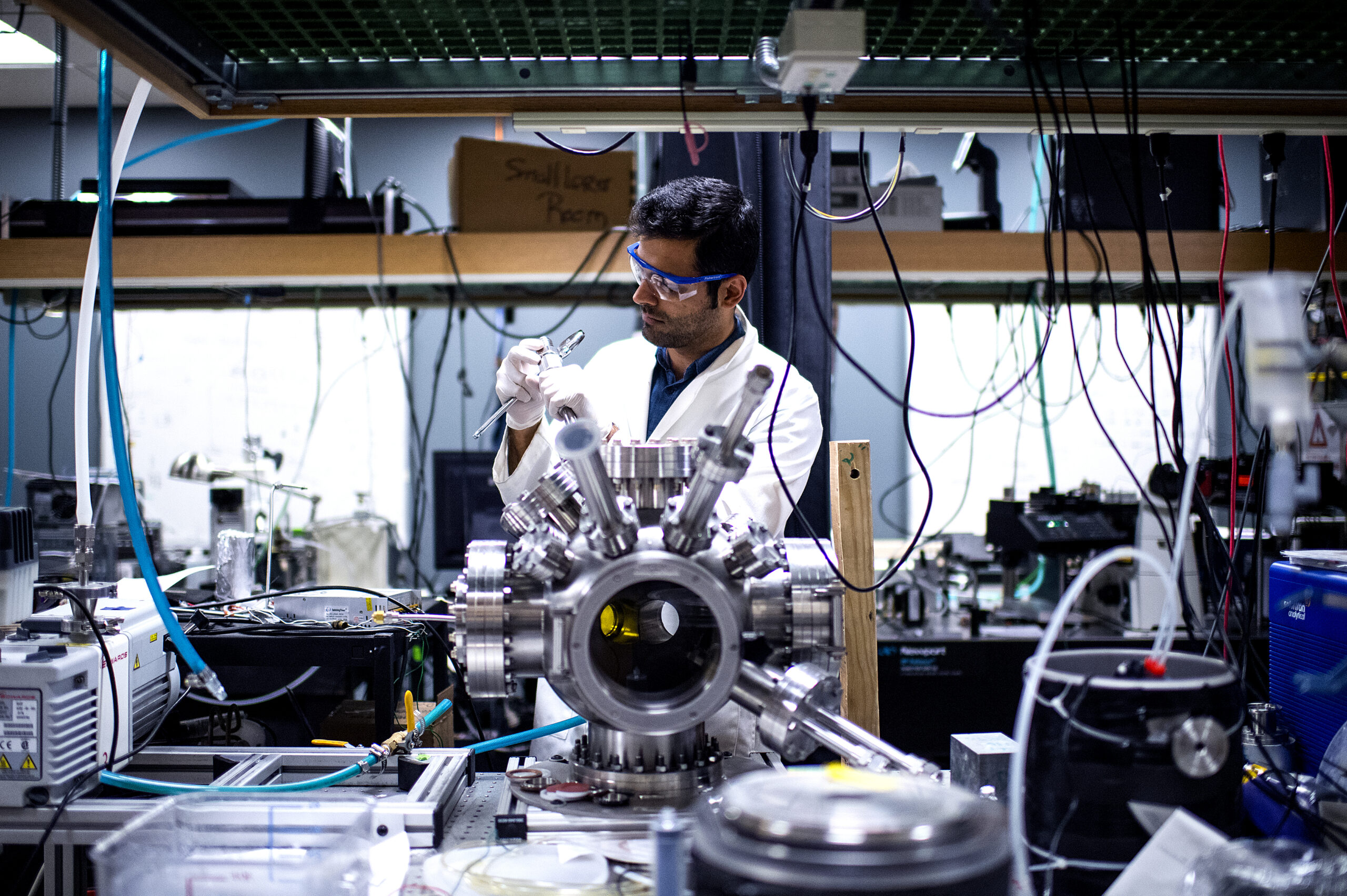
Wanunu receives $2M grant for ‘single-molecule’ protein identification
“Meni Wanunu, associate professor of physics and bioengineering affiliated faculty member, received a $2,000,000 R01 grant from the National Institutes of Health (NIH)/National Human Genome Research Institute (NHGRI) for ‘Asymmetric Single-Chain MspA Nanopores for Electroosmotic Stretching and Sequencing Proteins.’ … [Wanunu and collaborators] will develop a next-generation single-molecule protein sequencer based on engineered high-resolution nanopores. Protein identification and/or single-molecule protein sequencing from minute amounts could revolutionize our understanding of health by providing a picture of the molecular state of the cell at the level of its most functional molecules.”
-
Advancing distributed optimization for non-convex problems
“Mechanical and industrial engineering assistant professor Shahin Shahrampour has received a $500,000 NSF grant, in collaboration with Texas A&M University, to address ‘Consensus and Distributed Optimization in Non-Convex Environments With Applications to Networked Machine Learning.'”
-
Improving efficiency of data-centric computing
“Electrical and computer engineering professor Edmund Yeh was awarded a patent for ‘Network and Method for Servicing a Computation Request.'”
-
Minkara serves as moderator for intersection of disability panel
“Bioengineering assistant professor Mona Minkara served as a moderator for the ‘Intersection of Disability Panel’ at the Disrupting Ableism and Advancing STEM: A National Leadership Summit held on June 5, 2023.” Click on “Learn More” to watch the video.
-
Understanding cell transitions in tumor development
“University distinguished professor Herbert Levine, physics and bioengineering, in collaboration with Brown University and MD Anderson Cancer Center, is leading a $1,200,000 NSF grant for determining the ‘Regulation of Cellular Stemness During the Epithelial-Mesenchymal Transition (EMT).'”
-
‘Predictors and Consequences of Pro-Environmental Behavior at Work’
“Increasingly, people are looking for meaning through their jobs, for employers that have a positive impact on the world, and for workplaces that promote mission-driven behavior. One such mission that is a growing priority is addressing climate change, especially for younger cohorts entering the workforce. Addressing the climate crisis will necessitate substantial changes at all levels of society, including organizational change. This paper examines individual, social, and contextual variables that are associated with pro-environmental behavior (PEB).” Find the paper and full list of authors at ResearchGate.
-
‘Microbial Chemolithoautotrophs are Abundant in Salt Marsh Sediment Following Long-Term Experimental Nitrate Enrichment’
“Long-term anthropogenic nitrate (NO3−) enrichment is a serious threat to many coastal systems. Nitrate reduction coupled with the oxidation of reduced forms of sulfur is conducted by chemolithoautotrophic microbial populations in a process that decreases nitrogen (N) pollution. However, little is known about the diversity and distribution of microbes capable of carbon fixation within salt marsh sediment and how they respond to long-term NO3− loading. We used genome-resolved metagenomics to characterize the distribution, phylogenetic relationships, and adaptations important to microbial communities within NO3− enriched sediment.” Find the paper and full list of authors at FEMS Microbiology Letters.
-
‘Workforce Ecosystems and AI’
“Companies increasingly rely on an extended workforce (e.g., contractors, gig workers … and technologies such as algorithmic management and artificial intelligence) to achieve strategic goals and objectives. When we ask leaders to describe how they define their workforce today, they mention a diverse array of participants, beyond just full- and part-time employees, all contributing in various ways. … Our ongoing research on workforce ecosystems demonstrates that managing work across organizational boundaries with groups of interdependent actors in a variety of employment relationships creates new opportunities and risks for both workers and businesses.” Find the paper and full list of authors…
-
ACM Distinguished Papers Award for paper on adversarial attacks in deep learning models
“Computer engineering graduate students Ruyi Ding, PhD’24, Cheng Gongye, PhD’23, Siyue Wang, PhD’22, mathematics professor A. Adam Ding and electrical and computer engineering professor Yunsi Fei were awarded a Distinguished Papers Award at the 18th ACM ASIA Conference on Computer and Communications Security for their paper on ‘EMShepherd: Detecting Adversarial Samples via Side-channel Leakage.'”
-
Lin receives NSF grant for ‘Dynamic Scene Understanding’ in computer vision
“Electrical and computer engineering associate professor Xue ‘Shelley’ Lin, in collaboration with Khoury College of Computer Science assistant professor Huaizu Jiang, was awarded a $600K NSF grant for ‘Toward Efficient and Robust Dynamic Scene Understanding Based on Visual Correspondences.'”
-
‘A Tool for Mutation Analysis in Racket’
“Racket is a functional programming language that is used to teach CS1 at many high schools and colleges. … In order to evaluate [mutation analysis’s] efficacy in our college’s introductory programming courses, we created a prototype mutation analysis tool for Racket. We describe the design and features of the tool and perform a feasibility study using two assignments from an intro CS course where student test suite thoroughness was evaluated by hand by human graders.” Find the paper and full list of authors in the 2023 IEEE International Conference on Software Testing Verification and Validation Workshop.
-
‘SliceLens: Guided Exploration of Machine Learning Datasets’
“SliceLens is a tool for exploring labeled, tabular, machine learning datasets. To explore a dataset, the user selects combinations of features in the dataset that they are interested in. The tool splits those features into bins and then visualizes the label distributions for the subsets of data created by the intersections of the bins. SliceLens guides the user in determining which feature combinations to explore. Guidance is based on a user-selected rating metric, which assigns a score to the subsets created by a given combination of features.”
-
‘”Everyone is Covered”: Exploring the Role of Online Interactions in Facilitating Connection and Social Support in Black Churches’
“Faith institutions provide social support and community care for many in the United States (U.S.). Notably, churches with predominantly Black populations have served as a site for social change and care provision. … However, the pandemic has emphasised how localising these care networks in physical spaces can limit access to social support. … Through interviews and focus groups with nine church members, we explore how hybrid faith communities that bridge offline and online contexts can enable social support and care provision.” Find the paper and full list of authors in the 2023 CHI Conference on Human Factors in Computing Systems…
-
‘Game Level Blending Using a Learned Level Representation’
“Game level blending via machine learning, the process of combining features of game levels to create unique and novel game levels using Procedural Content Generation via Machine Learning (PCGML) techniques, has gained increasing popularity in recent years. However, many existing techniques rely on human-annotated level representations, which limits game level blending to a limited number of annotated games. … In this paper, we present a novel approach to game level blending … that can serve as a level representation for unannotated games and a unified level representation across games without … human annotation.” Find the paper and full list of…
-
‘Typed-Untyped Interactions: A Comparative Analysis’
“The literature presents many strategies for enforcing the integrity of types when typed code interacts with untyped code. This article presents a uniform evaluation framework that characterizes the differences among some major existing semantics for typed–untyped interaction. Type system designers can use this framework to analyze the guarantees of their own dynamic semantics.” Find the paper and full list of authors in ACM Transactions on Programming Languages and Systems.
-
‘EMShepherd: Detecting Adversarial Samples via Side-channel Leakage’
“Deep Neural Networks (DNN) are vulnerable to adversarial perturbations-small changes crafted deliberately on the input to mislead the model for wrong predictions. Adversarial attacks have disastrous consequences for deep learning-empowered critical applications. … Inspired by the fact that electromagnetic (EM) emanations of a model inference are dependent on both operations and data and may contain footprints of different input classes, we propose a framework, EMShepherd, to capture EM traces of model execution, perform processing on traces and exploit them for adversarial detection.” Find the paper and full list of authors at ArXiv.
-
‘Injecting Language Workbench Technology Into Mainstream Languages’
“Eelco Visser envisioned a future where DSLs become a commonplace abstraction in software development. He took strides towards implementing this vision with the Spoofax language workbench. However, his vision is far from the mainstream of programming today. How will the many mainstream programmers encounter and adopt language workbench technology? We propose that the macro systems found in emerging industrial languages open a path towards delivering language workbenches as easy-to-adopt libraries.” Find the paper and full list of authors at the Dagstuhl Research Online Publication Server.
-
‘Analysis of Catastrophic Forgetting for Random Orthogonal Transformation Tasks in the Overparameterized Regime’
“Overparameterization is known to permit strong generalization performance in neural networks. In this work, we provide an initial theoretical analysis of its effect on catastrophic forgetting in a continual learning setup. We show experimentally that in Permuted MNIST image classification tasks, the generalization performance of multilayer perceptrons trained by vanilla stochastic gradient descent can be improved by overparameterization, and the extent of the performance increase achieved by overparameterization is comparable to that of state-of-the-art continual learning algorithms.” Find the paper and full list of authors in the Proceedings of Machine Learning Research.
-
Enhancing security for brain-inspired computing
“Electrical and computer engineering assistant professor Xiaolin Xu, in collaboration with Shaolei Ren from the University of California-Riverside, was awarded a $600,000 NSF grant for ‘Securing Brain-inspired Hyperdimensional Computing against Design-time and Run-time Attacks for Edge Devices.'”