Title
Topic
-
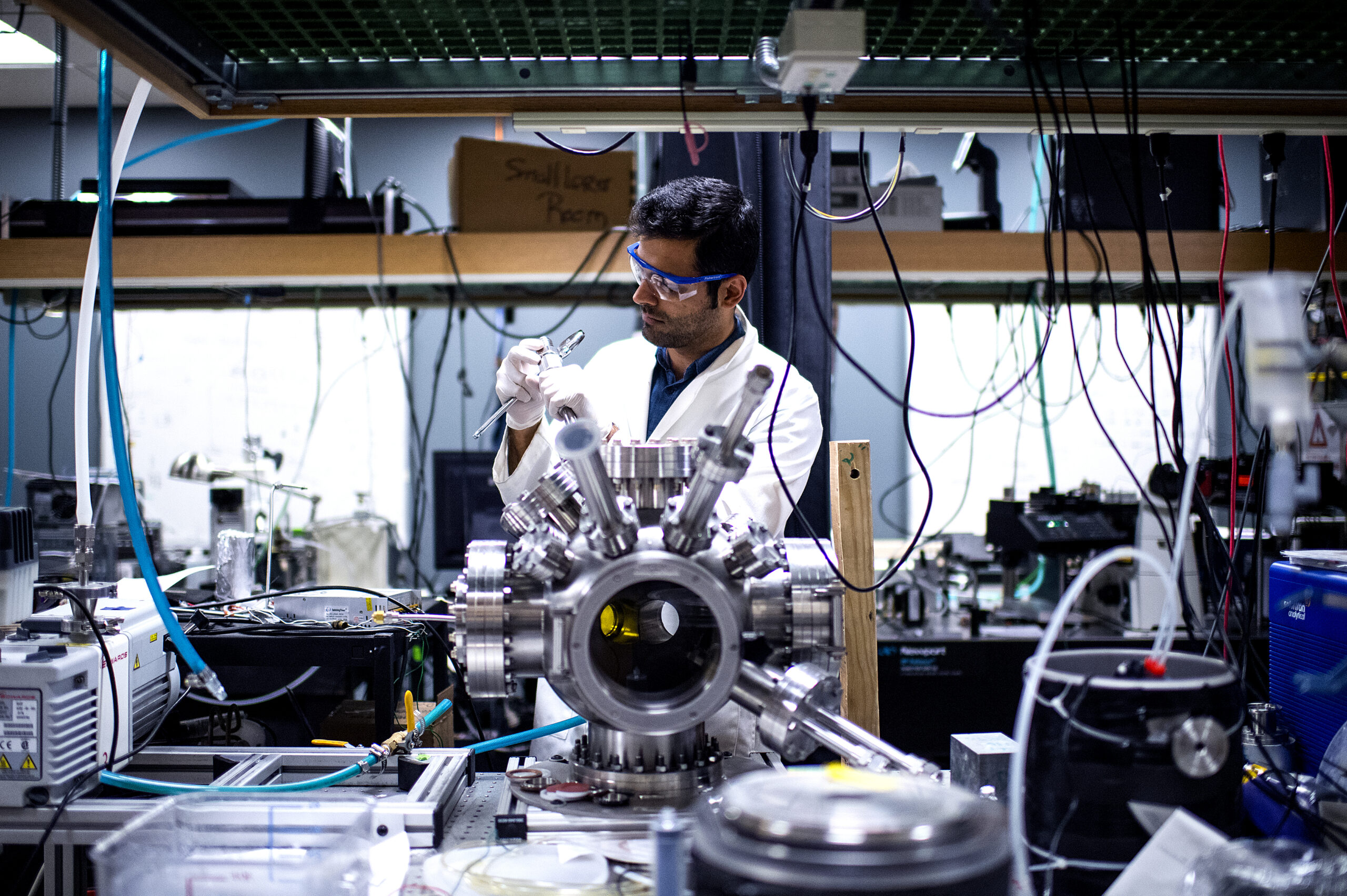
Improving power delivery for high-performance computing
“Electrical and computer engineerings professor Nian Sun and associate professor Aatmesh Shrivastava, in collaboration with Khurram Afridi and Huili (Grace) Xing from Cornell University, were awarded a $2,000,000 NSF grant for ‘Heterogeneous Integration in Power Electronics for High-Performance Computing (HIPE-HPC).’ This grant was awarded as part of the NSF Future of Semiconductors (FuSe) program.”
-
‘A Large Scale Analysis of Semantic Versioning in NPM’
“The NPM package repository contains over two million packages and serves tens of billions of downloads per-week. Nearly every single JavaScript application uses the NPM package manager to install packages from the NPM repository. NPM relies on a ‘semantic versioning’ (‘semver’) scheme to maintain a healthy ecosystem, where bug-fixes are reliably delivered to downstream packages as quickly as possible. … In order to understand how developers use semver, we build a dataset containing every version of every package on NPM and analyze the flow of updates throughout the ecosystem.” Find the paper and full list of authors at ArXiv.
-
‘Improving Cross-Domain Detection with Self-Supervised Learning’
“Cross-Domain Detection (XDD) aims to train a domain-adaptive object detector using unlabeled images from a target domain and labeled images from a source domain. Existing approaches achieve this either by transferring the style of source images to that of target images, or by aligning the features of images from the two domains. In this paper, rather than proposing another method following the existing lines, we introduce a new framework complementary to existing methods.” Find the paper and full list of authors in the IEEE Computer Society Conference on Computer Vision and Pattern Recognition Workshops.
-
‘Trainability Preserving Neural Pruning’
“Many recent works have shown trainability plays a central role in neural network pruning — unattended broken trainability can lead to severe under-performance and unintentionally amplify the effect of retraining learning rate, resulting in biased (or even misinterpreted) benchmark results. This paper introduces trainability preserving pruning (TPP), a scalable method to preserve network trainability against pruning, aiming for improved pruning performance and being more robust to retraining hyper-parameters (e.g., learning rate).” Find the paper and full list of authors at Open Review. Published at ICLR 2023.
-
‘Sharing Speaker Heart Rate With the Audience Elicits Empathy and Increases Persuasion’
“Persuasion is a primary goal of public speaking, and eliciting audience empathy increases persuasion. In this research, we explore sharing a speaker’s heart rate as a social cue, to elicit empathy and increase persuasion in the audience. In particular, we developed two interfaces embedding the speaker’s heart rate over a recorded presentation video. … We observed that heart rate sharing significantly increased persuasion for participants with normal baseline empathy levels and increased empathic accuracy for all participants.” Find the paper and full list of authors in the journal of the International Conference on Persuasive Technology.
-
‘Sturgeon-GRAPH: Constrained Graph Generation From Examples’
“Procedural level generation techniques that learn local neighborhoods from example levels (such as WaveFunctionCollapse) have risen in popularity. Usually the neighborhood structure (such as a regular grid) onto which a level is generated is fixed in advance and not generated. In this work, we present a constraint-based approach for graph generation that learns local neighborhood patterns (in the form of labeled nodes and edges) from example graphs. This allows the approach to generate graphs with varying structures that are still locally similar to the examples.”
-
‘LRPRNet: Lightweight Deep Network by Low-Rank Pointwise Residual Convolution’
“Deep learning has become popular in recent years primarily due to powerful computing devices such as graphics processing units (GPUs). However, it is challenging to deploy these deep models to multimedia devices, smartphones, or embedded systems with limited resources. To reduce the computation and memory costs, we propose a novel lightweight deep learning module by low-rank pointwise residual (LRPR) convolution, called LRPRNet.” Find the paper and full list of authors at IEEE Transactions on Neural Networks and Learning Systems.
-
‘Principles and Guidelines for Evaluating Social Robot Navigation Algorithms’
“A major challenge to deploying robots widely is navigation in human-populated environments, commonly referred to as social robot navigation. While the field of social navigation has advanced tremendously in recent years, the fair evaluation of algorithms that tackle social navigation remains hard. … In contrast, clear, repeatable, and accessible benchmarks have accelerated progress in fields like computer vision, natural language processing and traditional robot navigation. … In this paper, we pave the road towards common, widely accessible, and repeatable benchmarking criteria to evaluate social robot navigation.” Find the paper and full list of authors at ArXiv.
-
‘Using Overlapping Methods To Counter Adversaries in Community Detection’
“When dealing with large graphs, community detection is a useful data triage tool that can identify subsets of the network that a data analyst should investigate. In an adversarial scenario, the graph may be manipulated to avoid scrutiny of certain nodes by the analyst. Robustness to such behavior is an important consideration for data analysts in high-stakes scenarios such as cyber defense and counterterrorism. In this paper, we evaluate the use of overlapping community detection methods in the presence of adversarial attacks aimed at lowering the priority of a specific vertex. Find the paper and full list of authors at…
-
‘Fast and Simple Solutions of Blotto Games’
“The Colonel Blotto game is commonly used for analyzing a wide range of applications from the U.S. Presidential election to innovative technology competitions to advertising, sports, and politics. There are persistent efforts to find the optimal strategies for the Colonel Blotto game. However, the first polynomial-time algorithm for that has very recently been provided by Ahmadinejad, [et al.]. … In this paper, we provide the first polynomial-size LP formulation of the optimal strategies for the Colonel Blotto game using linear extension techniques.” Find the paper and full list of authors at Operations Research.
-
‘The Pseudorandom Oracle Model and Ideal Obfuscation’
“We introduce a new idealized model of hash functions, which we refer to as the pseudorandom oracle (PrO) model. Intuitively, it allows us to model cryptosystems that use the code of an ideal hash function in a non-black-box way. Formally, we model hash functions via a combination of a pseudorandom function (PRF) family and an ideal oracle. A user can initialize the hash function by choosing a PRF key k and mapping it to a public handle h using the oracle.” Find the paper and full list of authors in Advances in Cryptology.
-
Global strategic partnership forged to advance robotic technology
“Electrical and computer engineering assistant professor Alireza Ramezani is collaborating on a $3,000,000 project with Caltech as part of a cross-disciplinary collaboration focused on the design and control of multi-modal robots. This collaboration aims to address the critical areas of disaster response and package delivery within the framework of a multi-million dollar project funded by the Technology Innovation Institute of Abu Dhabi in Dubai.”
-
‘Experimental Security Analysis of DNN-Based Adaptive Cruise Control Under Context-Aware Perception Attacks’
“Adaptive Cruise Control (ACC) is a widely used driver assistance feature for maintaining desired speed and safe distance to the leading vehicles. This paper evaluates the security of the deep neural network (DNN) based ACC systems under stealthy perception attacks that strategically inject perturbations into camera data to cause forward collisions. We present a combined knowledge-and-data-driven approach to design a context-aware strategy for the selection of the most critical times for triggering the attacks and a novel optimization-based method for the adaptive generation of image perturbations at run-time.” Find the paper and full list of authors at ArXiv.
-
‘Calculational Proofs in ACL2s’
“Teaching college students how to write rigorous proofs is a critical objective in courses that introduce formal reasoning. Over the course of several years, we have developed a mechanically-checkable style of calculational reasoning … to teach over a thousand freshman-level undergraduate students how to reason about computation in our ‘Logic and Computation’ class at Northeastern University. … Our calculational proof checker is integrated into ACL2s and is available as an Eclipse IDE plugin, via a Web interface and as a stand-alone tool. It automatically checks proofs for correctness and provides useful feedback.” Find the paper and full list of authors…
-
‘Diagnosing Human-Object Interaction Detectors’
“In this paper, we introduce a diagnosis toolbox for analyzing the error sources of the existing [human-object interaction] HOI detection models. We first conduct holistic investigations in the pipeline of HOI detection. … We define a set of errors and the oracles to fix each of them. By measuring the [mean Average Precision] mAP improvement obtained from fixing an error using its oracle, we can have a detailed analysis of the significance of different errors. We then delve into the human-object detection and interaction classification, respectively, and check the model’s behavior.” Find the paper and full list of authors at…
-
‘Scaling Integer Arithmetic in Probabilistic Programs’
“Distributions on integers are ubiquitous in probabilistic modeling but remain challenging for many of today’s probabilistic programming languages (PPLs). … Our insight is that there is structure in arithmetic that these approaches are not using. We present a binary encoding strategy for discrete distributions that exploits the rich logical structure of integer operations like summation and comparison. We leverage this structured encoding with knowledge compilation to perform exact probabilistic inference, and show that this approach scales to much larger integer distributions with arithmetic.” Find the paper and full list of authors at ArXiv.
-
‘Designing for Playfulness in Human-AI Authoring Tools’
“Many human-AI authoring tools are used in a playful way, while being primarily designed for task-achievement—not playfulness. We argue that playfulness is an important yet overlooked factor of user behaviour and experience when interacting with such tools. … In this paper, we motivate the importance of playfulness as user experience in human-AI authoring tools, and propose concrete strategies to design for playfulness in the human user through UI design, in the AI through algorithms or through interventions to their dialog.” Find the paper and full list of authors in the 18th International Conference on the Foundations of Digital Games proceedings.
-
‘Knowledge Transfer From High-Resource to Low-Resource Programming Languages for Code LLMs’
“Over the past few years, Large Language Models of Code (Code LLMs) have started to have a significant impact on programming practice. Code LLMs are also emerging as a building block for research in programming languages and software engineering. However, the quality of code produced by a Code LLM varies significantly by programming languages. … This paper presents an effective approach for boosting the performance of Code LLMs on low-resource languages using semi-synthetic data. Our approach generates high-quality datasets for low-resource languages, which can then be used to fine-tune any pretrained Code LLM.” Find the paper and list of authors…
-
‘Contrastive Alignment of Vision to Language Through Parameter-Efficient Transfer Learning’
“Contrastive vision-language models (e.g. CLIP) are typically created by updating all the parameters of a vision model and language model through contrastive training. Can such models be created by a small number of parameter updates to an already-trained language model and vision model? … We explore the feasibility and benefits of parameter-efficient contrastive vision-language alignment through transfer learning: creating a model such as CLIP by minimally updating an already-trained vision and language model. We find that a minimal set of parameter updates (<7%) can achieve the same performance as full-model training.” Find the paper and full list of authors at…
-
‘Frame Flexible Network’
“Existing video recognition algorithms always conduct different training pipelines for inputs with different frame numbers, which requires repetitive training operations and multiplying storage costs. If we evaluate the model using other frames which are not used in training, we observe the performance will drop significantly. … To fix this issue, we propose a general framework, named Frame Flexible Network (FFN), which not only enables the model to be evaluated at different frames to adjust its computation, but also reduces the memory costs of storing multiple models significantly.” Find the paper and full list of authors at ArXiv.
-
‘Robust Communication Complexity of Matching: EDCS Achieves 5/6 Approximation’
“We study the robust communication complexity of maximum matching. Edges of an arbitrary n-vertex graph G are randomly partitioned between Alice and Bob independently and uniformly. Alice has to send a single message to Bob such that Bob can find an (approximate) maximum matching of the whole graph G. We specifically study the best approximation ratio achievable via protocols where Alice communicates only O˜(n) bits to Bob.” Find the paper and full list of authors at ArXiv.
-
‘Streaming Edge Coloring with Asymptotically Optimal Colors’
“Given a graph G, an edge-coloring is an assignment of colors to edges of G such that any two edges sharing an endpoint receive different colors. By Vizing’s celebrated theorem, any graph of maximum degree Δ needs at least Δ and at most (Δ+1) colors to be properly edge colored. In this paper, we study edge colorings in the streaming setting. The edges arrive one by one in an arbitrary order. The algorithm takes a single pass over the input and must output a solution using a much smaller space.” Find the paper and full list of authors at ArXiv.
-
‘BEV-DG: Cross-Modal Learning Under Bird’s-Eye View for Domain Generalization of 3D Semantic Segmentation’
“Cross-modal Unsupervised Domain Adaptation (UDA) aims to exploit the complementarity of 2D-3D data to overcome the lack of annotation in a new domain. However, UDA methods rely on access to the target domain during training, meaning the trained model only works in a specific target domain. In light of this, we propose cross-modal learning under bird’s-eye view for Domain Generalization (DG) of 3D semantic segmentation, called BEV-DG. … Our approach aims to optimize domain-irrelevant representation modeling with the aid of cross-modal learning under bird’s-eye view.” Find the paper and full list of authors at ArXiv.
-
Developing eco-friendly cooling solutions
“Mechanical and industrial engineering associate professor Yi Zheng’s spinout from his lab at Northeastern, Planck Energies, has received a $275,000 NSF grant for ‘Climate-Eco-Friendly Biocoating for Passive Cooling of Infrastructure.'”
-
Dahiya speaks at AI for Good Global Summit
“Electrical and computer engineering professor Ravinder Dahiya was selected as a speaker for the AI for Good Global Summit: Accelerating the United Nations Sustainable Development Goals, which was held in Geneva, Switzerland, July 6-7, 2023. The AI for Good Global Summit is the leading action-oriented United Nations platform promoting AI to advance health, climate, gender, inclusive prosperity, sustainable infrastructure and other global development priorities.”
-
Psychology professor building ‘data science tool’ to increase the reliability of human brain research
Assistant professor of psychology Stephanie Noble is building a power calculator to help human neuroscience researchers increase the reproducibility of their experiments.
-
Researchers win best paper award for content distribution framework
“A team of researchers from Northeastern University, MIT and EURECOM won the best paper award at the 21st International Symposium on Modeling and Optimization in Mobile, Ad-hoc and Wireless Networks (WiOpt 2023) for their paper on ‘Joint Optimization of Storage and Transmission via Coding Traffic Flows for Content Distribution.'”
-
Landherr wins Best ChemE Division Paper at Annual ASEE Conference
“Chemical engineering teaching professor and associate chair of undergraduate studies Luke Landherr was named to receive the Joseph J. Martin Award for the most outstanding Chemical Engineering Division paper presented at the 2023 ASEE Annual Conference. Their paper, entitled ‘Teaching Fugacity Through Comics and Assessing the Impact on Student Confidence and Understanding,’ is based on their research using comics as visual learning tools in undergraduate education.”