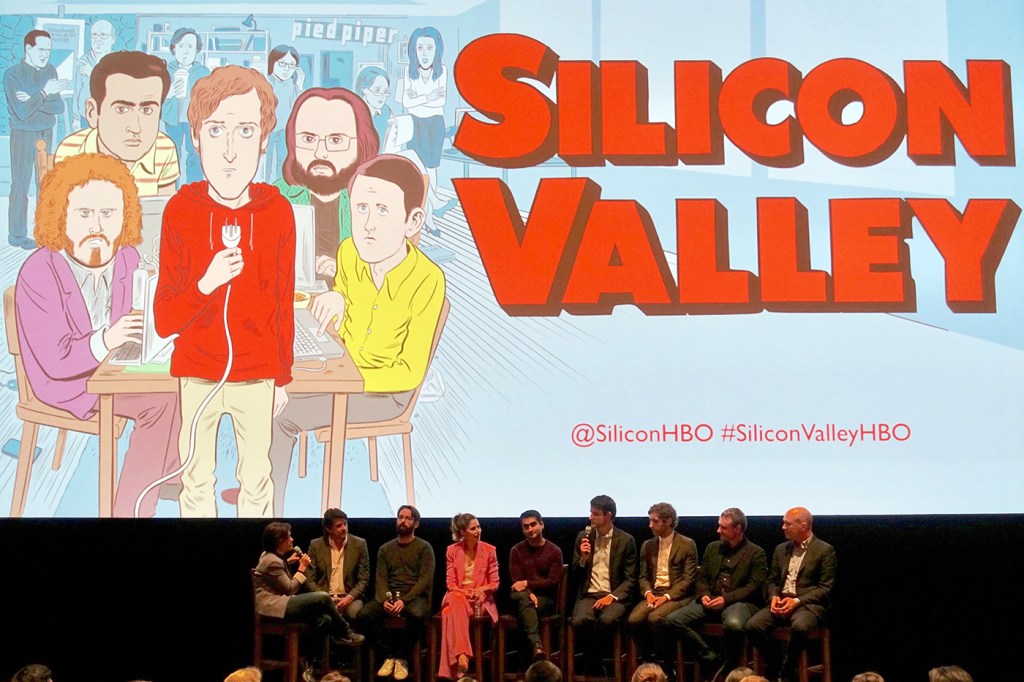
Could the tech snafu in Silicon Valley’s finale actually happen?
In the finale of the fourth season of HBO’s Silicon Valley, we find the Pied Piper gang facing the consequences of their quest for technological relevance—namely, what to do when the software they sneaked onto people’s phones was causing those phones to overheat and explode, and how to tap into data that was fortuitously (and accidentally) stored on a network of smart refrigerators.
But let’s back up. (And fair warning, spoilers ahead.)
For the uninitiated, Silicon Valley is a show that centers on six friends who launch a startup internet company, Pied Piper, with dreams of striking it rich. In the latest season, the founders focus on creating a peer-to-peer internet system, the implementation of which drives conflict after conflict in the show.
As it often does, fiction mirrors reality, and Silicon Valley is no exception. “Hooli” is a tech giant in the vein of Google or Microsoft; and the characters referenced an issue with Samsung phones that caused the batteries to overheat and catch fire. But as is also often the case, the showrunners push the limits of reality to the extreme, leaving audiences to wonder, ‘Could that actually happen?’
So, we asked someone who would know.
David Choffnes, assistant professor in the College of Computer and Information Science, studies distributed networks and networking and has more recently focused on mobile systems. He’s also a fan of Silicon Valley.
And while topics in past seasons of the show have touched on some aspects of his expertise, the most recent season “hit the closest,” he said.
For example, Pied Piper’s quest to create a peer-to-peer network is something with which Choffnes is very familiar—he actually worked at a startup that sought to do the same thing.
“Peer-to-peer is best defined by what it isn’t,” Choffnes explained. “The traditional model works like this: If you want to watch a video on YouTube, your computer goes to a Google server to request that video, and the server serves you that data. So, all you do is request things, and the server’s only job is to serve you content.”
In peer-to-peer networks, though, it’s a two-way street.
“The idea is that you don’t have to rely on Google or Microsoft that have servers to host content. You upload pieces of a large file yourself, you upload it to other people like you who have normal devices, and all those pieces can be reassembled by someone else,” he said.
In the show, the Pied Piper gang tricks attendees of a Hooli conference into downloading its app by diverting them to a specific download page when people try to connect to the internet at the conference. While not impossible, pulling off such a hack, according to Choffnes, seems “impractical.” As the logic goes, the more computers hosting data, the more information that can be stored.
The particular app that Pied Piper is pawning is designed to compress existing data to make room for storing the peer-to-peer, shared data. This, Choffnes said, is a hook that’s “particular to this plotline.” In other words, peer-to-peer sharing isn’t new, but Pied Piper’s compression app is.
So, while the theory behind this season’s plot—that a decentralized, peer-to-peer internet exists and could change the future of the internet—is sound, there were aspects of the season finale that “stretched reality,” Choffnes said.
Near the end of the episode, a supercomputer housing all of Pied Piper’s proprietary data falls off the back of a truck. With the computer and the data gone, it seems all of the company’s hopes for success are also gone. In a twist, however, it’s discovered that the data lives on, in a network of internet-connected, “smart” refrigerators, and the team is back in business.
Choffnes said that this plotline is where things get tricky.
The first aspect of the show that stretched reality is in how much data is purportedly stored on this network of smart refrigerators.
Some backstory: Earlier in the season, as a prank, one character hacked another’s fridge so it would play an inappropriate video. In order to do so, he installed the Pied Piper software on that smart fridge to compress the existing fridge data and make room for the video.
What he didn’t expect, though, was that once that software was installed, the smart fridge would become part of the peer-to-peer network Pied Piper was building, storing data in the empty space left over after compression. Later, this would turn out to be pivotal—the data stored on this, and other internet-connected smart refrigerators, essentially backed up the massive amount of data that had been on the supercomputer before it was smashed to smithereens.
While a fun twist in the show, Choffnes said this seems an unlikely solution.
“How much data could they really store on these smart refrigerators if they had trouble fitting a video on the thing? I can’t imagine it would store much more,” he said. “It seems unlikely that these devices would be useful for storing that much data.”
The second scenario that seems unlikely, Choffnes said, is in how this software spread to an entire network of smart refrigerators. In the show, we discover that the Pied Piper software is misinterpreted by the refrigerator as an update and, as such, downloaded in every smart refrigerator of the same model—a network of thousands of computers.
However, Choffnes said, “that kind of self-correcting software doesn’t exist.” The sorts of internet-connected devices like the smart fridges in question fall into the internet of things category. Many of these types of devices don’t ever get updated, Choffnes said.
“A smart fridge may have updates, but it would go through a central server,” Choffnes said, which would prevent “these fridges from becoming a rogue target like in the case of what happened in the show.”
The way it’s presented in Silicon Valley “just isn’t very plausible,” he said.





